
Are Your IoT Devices Putting Your Business or Your Customers at Risk?
Nearly half of all companies in the US using an Internet of Things (IoT) network have been the victims of at least one security breach. Forty-eight percent. That’s according to a recent survey of 400 IT decision-makers across 19 industries conducted by strategy consulting group Altman Vilandrie & Company.
What kind of breaches? Here are just two examples:
- An attack on a Vegas casino reported by cyber security firm Darktrace in July 2017. In that event, hackers swiped 10 gigabytes of data by accessing the casino’s network through a recently installed smart fish tank. The internet connection was supposed to allow casino workers to remotely monitor the tank, automate feedings and adjust the temperature but instead provided entrée for some very enterprising virtual thieves.
- Using malware, hackers acquired personal data for more than 70 million Target customers by penetrating an internet-connected computer at one of the company’s subcontractors, a small HVAC firm with minimal security. After easily stealing the subcontractor’s login, the hackers were able to access Target’s network.
Devices Under Attack
We’ve quickly come a long way from the days hackers frightened a few unsuspecting parents, spying on their toddlers via seemingly innocuous baby monitors. Today, IoT breaches are commonplace and increasingly sinister — and a major concern not just for consumers drawn to smart devices to ease their daily lives, but for the vast number of businesses that rely on the internet to operate. And, of course, for device manufacturers themselves.
Many of the connected devices for sale today are seriously lacking when it comes to security. They're under constant attack from the moment they're hooked up to the internet and can fall under hacker control within minutes. — IBM Security and Ponemon Institute
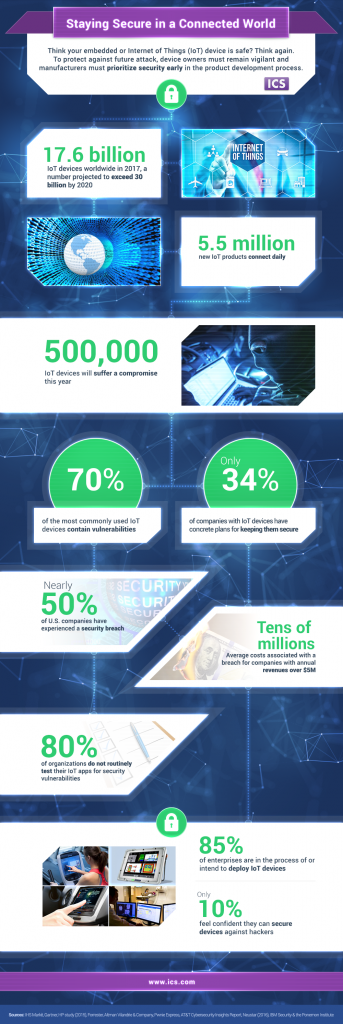
From smartphones and tablets to video cameras and printers to industrial controls and sensitive medical equipment, today there are more than 17 million IoT devices in use worldwide — a number expected to reach 30.7 million by 2020. And with every single device comes risk.
Not only can breaches compromise users’ sensitive data, like social security numbers, banking information or medical records, they can even expose users to physical risk — say a zero-day exploit similar to the pre-choreographed one unleashed on a Jeep Cherokee in 2015. In that episode, hackers thousands of miles away used malicious software to gain remote control of the Jeep’s in-vehicle entertainment system — while the car was in motion — comandeering the vehicle’s steering, brakes, transmission and dashboard functions as the driver sat by helplessly.
For consumers, breaches can be terrifying. For businesses, costly. For companies with annual revenues over $5 million, average costs associated with a breach run into the tens of millions, according to IBM. And some of those costs are uninsurable, like a company’s good reputation and healthy market share, which can disappear with lightning speed as wary customers flock to seemingly more secure competitors.
Improving Security of Connected Devices
According to Health IT Infrastructure, any IoT device can have a security vulnerability that could potentially affect the entire network. For instance, they note that vulnerabilities have been found in defibrillators, pacemakers and diabetes insulin pumps, which have inadvertently broadcast signals to the internet rather than communicating only with the management server as intended.
With such a high degree of risk associated with IoT devices — when even something as mundane as the office’s smart coffeemaker could potentially expose a corporate network via an unprotected gateway — why isn’t there greater device security?
Here’s why.
We live in a modern Gold Rush era when each day 5.5 million new IoT products connect to the internet. A time when the race among manufacturers to get to market first and cash in on consumers’ insatiable appetite for connected devices is intense. When the IoT and the industrial Iot (IIoT) are integral to corporate business operations.
Developers are under pressure by manufacturers to code faster to keep up with skyrocketing demand. They simply don’t have much time in the product development lifecycle to devote to security since speed to market is their priority. Even with the luxury of time, these same manufacturers often prioritize adding new features over strengthening security.
Not to mention the fact that for inexpensive devices — say a $30 smart thermostat — manufacturers may not have large enough margins to make incorporating expensive security a business decision that makes sense to them.
Of course, this is precisely why businesses that use connected devices need to harden their networks, and manufacturers need to step up their game in terms of designing in better security.
ICS has developed and tested hundreds of successful IoT devices and IIoT industrial controls. In my next blog I'll share a few of the ways manufacturers and enterprises can boost security.